Trezor Login: Your Safe Passage Into the Crypto World
Experience the unmatched security of Trezor login. Learn how this simple yet powerful authentication process keeps your digital assets safe, private, and fully under your control.
Understanding the Power of Trezor Login
Trezor login is not just another sign-in screen; it’s a bridge between your physical crypto wallet and your online activity. By using a hardware device for authentication, Trezor ensures that your keys never touch the internet — a fundamental step in true crypto self-custody.
Unlike conventional login systems where data lives on cloud servers, Trezor decentralizes access. It gives you exclusive ownership, meaning your crypto cannot be moved, accessed, or tampered with without your consent.
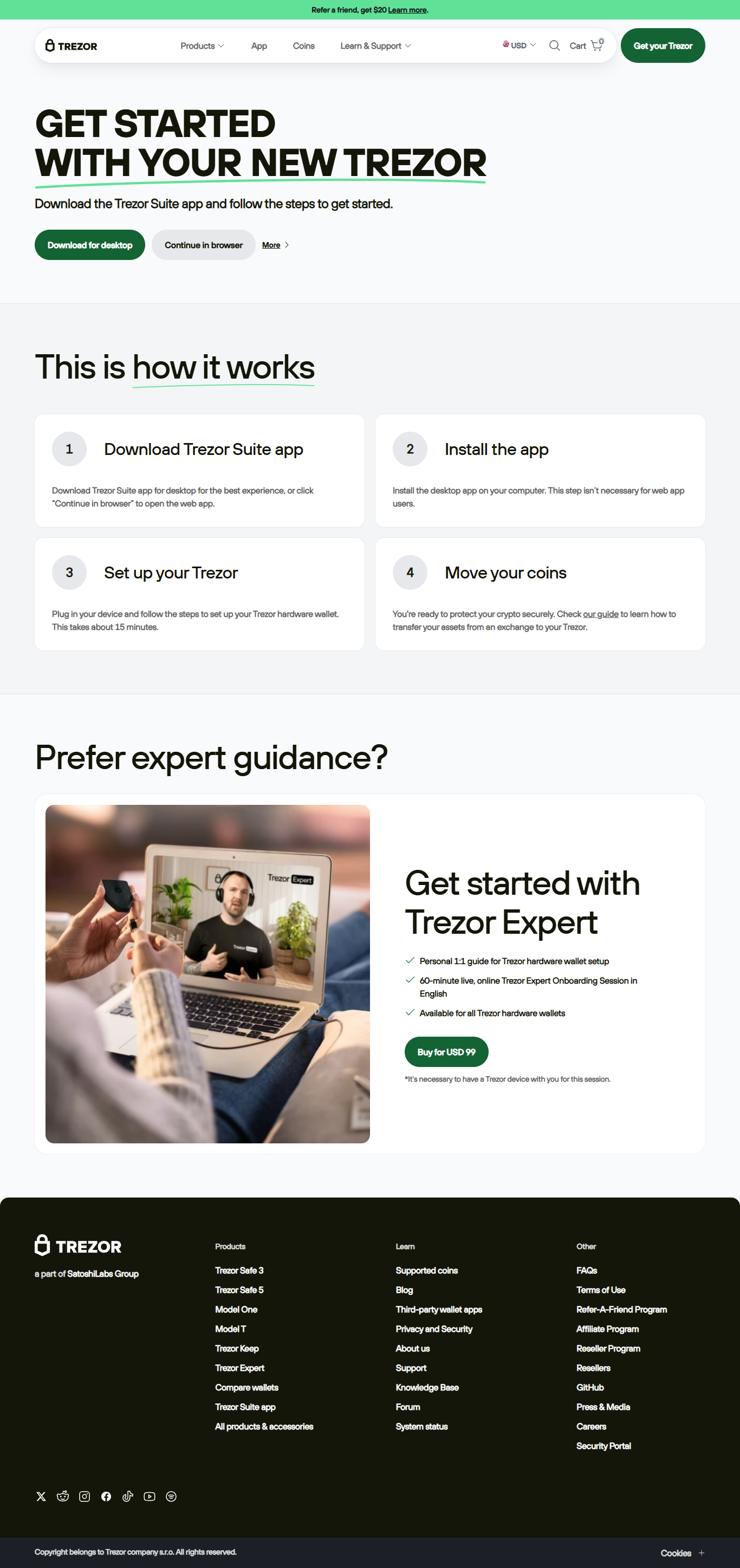
Step-by-Step: How to Use Trezor Login
1. Connect Your Device
Start by plugging in your Trezor device using its original cable. Allow your computer to recognize it through Trezor Bridge.
2. Launch Trezor Suite
Open the Trezor Suite app. It automatically detects your connected device and initiates the secure login protocol.
3. Confirm Authentication
On your Trezor device’s screen, verify the login request. No credentials are ever typed or transmitted over the internet.
4. Access Your Dashboard
Once confirmed, your wallet and portfolio are unlocked for secure transactions, tracking, and account management.
Why Choose Trezor Login?
The Trezor login system is built for those who prioritize privacy, safety, and independence. Here’s what makes it exceptional:
- 🛡️ Hardware-based Protection: Private keys remain offline, shielded from hackers and malware.
- 💡 User-First Design: Clean, simple, and intuitive authentication for all experience levels.
- 🧩 Open-Source Software: Transparency ensures constant community-driven security checks.
- 🚀 Cross-Chain Support: Manage Bitcoin, Ethereum, and multiple altcoins seamlessly.
Common Issues During Trezor Login & Fixes
Device Not Detected
Ensure Trezor Bridge is installed. Switch USB ports or browsers if necessary. Avoid USB hubs for initial setup.
PIN Forgotten
You’ll need to reset the device using your recovery seed. Always keep your 12–24 word seed phrase offline and safe.
Firmware Outdated
Open Trezor Suite and follow the on-screen update instructions to ensure compatibility and maximum protection.
Trezor Login vs. Traditional Crypto Logins
| Feature | Trezor Login | Exchange Login |
|---|---|---|
| Authentication Type | Hardware-secured | Password-based |
| Private Key Control | User-owned | Custodial |
| Vulnerability Risk | Minimal | High |
| Data Storage | Local & Encrypted | Cloud-based |
Trezor Login FAQ
1. Is Trezor login safe for beginners?
Yes, the process is beginner-friendly and designed to make crypto security accessible to everyone.
2. Can I use Trezor login without Trezor Suite?
While possible via supported browsers, Trezor Suite is the recommended environment for optimal security.
3. What if I lose my Trezor device?
You can restore access using your recovery seed on a new device. The seed phrase is your ultimate safeguard.
4. Do I need the internet for Trezor login?
Yes, but your private keys remain offline even during online login attempts.
Trezor Login — Secure, Simple, and Smart
When you use Trezor login, you’re not just accessing your crypto wallet — you’re exercising control, privacy, and independence. Let your keys stay yours forever.